Cyber Attacks and the Problem of Attribution
This article explores the question of attribution for cyber attacks and offers potential solutions to ease the process of attribution

This article explores the question of attribution for cyber attacks and offers potential solutions to ease the process of attribution

This article analyses whether computer data can be considered an object under International Humanitarian Law (IHL)

This article examines the defintion of a cyber attack and its potential regulation of a cyber attack under IHL’s general principles

This article identifies three major areas of consideration that create differences in determining policies for cyber security

This editorial explores the questions that the international community needs to answer in determining how the laws of war apply in cyberspace

This article explores the hyper around strategic non-nuclear weapons and analyses their benefit to a country’s military arsenal
This article explores the rise of Strategic Non-Nuclear Weapons, their transformative technologies, and the need for non-proliferation in a shifting security landscape.
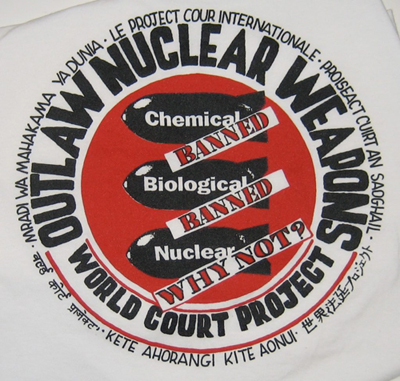
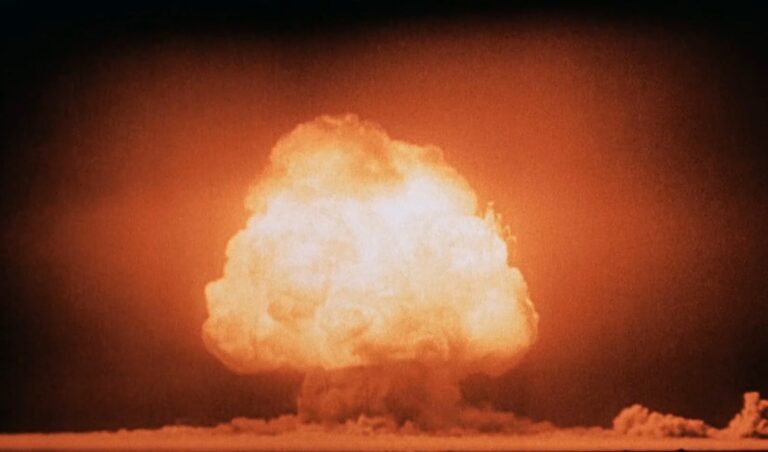
This article analyses ICJ’s Advisory Opinion on the Threat or Use of Nuclear Weapons

This article aims to explore the complex relationship between nuclear weapons, deterrence, and their potential influence on conflicts.

This article explores the prospects of a nuclear-free world in light of different policy approaches to nuclear non-proliferation
End of content
End of content